Digital risks grow, but our security
outpaces. Stay cyber-protected with
Hacker Associate
Stay ahead of cyber threats and fortify your digital assets with Hacker Associate.
Get started







Training
We provide expert-led cybersecurity training on ethical hacking, compliance, risk management, and cyber threat intelligence, building a resilient, security-first mindset that will help them new-age cyber challenges.
Know MoreServices
We provide a full spectrum of security measures, including threat detection, penetration testing, incident response, and risk assessment, to ensure solid security against ever-changing portrayals of cyber threats for businesses of all sizes.
Know MoreRND
Our Cyber Security R&D, with a focus on threat detection and analysis of malware and advanced encryption techniques, continuously aims to stay ahead of cybercriminals to ensure that the future of digital security remains an assured horizon.
Know MoreIntelligence Bureau
We deliver real-time cyber threat intelligence by monitoring dark web activities, data breaches, and emerging threats, allowing us to formulate proactive defense strategies that protect crucial business infrastructure.
Know MoreAbout Hacker Associate
We are a leading cybersecurity training and VAPT service provider, delivering cutting-edge cybersecurity services, hands-on VAPT solutions, and expert-led workshops for private and government organizations worldwide. As India’s only institute with 80+ cybersecurity certification programs, we emphasize practical learning and real-world case studies to equip professionals with the required skills.
Our high-profile training programs are led by a Chief Information Security Officer (CISO) with 50+ penetration testing certifications, ensuring unparalleled expertise.
From our inception as a specialized training institute to becoming a leader in cybersecurity education and services, we have trained thousands of students, professionals, and organizations. Today, Hackers Associate stands as a trusted name in cybersecurity, strengthening India’s and the world’s cyber defense with top-tier training and security solutions.

Our Services
CyberProof Your Business With
Hacker Associate
Cybersecurity That Actually Protects
We help businesses detect threats early, respond quickly, and stay protected with modern security solutions.
Managed Detection and Response (MDR)
Our MDR service offers 24/7 threat monitoring, rapid detection, and immediate response to cyber threats. By combining the latest technology and expert analysis, we proactively safeguard your organization from evolving cybersecurity risks.
Incident Response
When a cyber incident occurs, our expert team acts immediately to contain the threat, investigate the breach, and restore operations. We minimize downtime and safeguard your business from further damage.
Endpoint Protection (EPaaS)
Our Endpoint Protection as a Service (EPaaS) delivers AI-powered threat prevention, real-time malware defense, and continuous monitoring to secure all endpoints, keeping your organization protected from cyber threats.
Patch Management (PMaaS)
With our Patch Management as a Service (PMaaS), critical security updates are automated, ensuring your systems remain secure, compliant, and resilient by promptly addressing vulnerabilities.
Data Protection / Immutable Storage
At Hacker Associate, we offer tamper-proof, immutable storage solutions that prevent unauthorized modifications, ensuring data integrity, resilience against ransomware, and uninterrupted business continuity.
Zero Trust Network Access (ZTNA)
Our Zero Trust Network Access (ZTNA) solutions enforce strict identity verification and least-privilege access, securing your network with authenticated, encrypted connections and eliminating unauthorized access risks.
Cloud Penetration Testing
Our Cloud Penetration Testing services identify vulnerabilities in your cloud infrastructure, providing detailed risk assessments and actionable insights to strengthen security and protect sensitive data.
Master ethical hacking and penetration testing with OHSE
The Offensive Hacking Security Expert (OHSE) course equips you with advanced penetration testing, ethical hacking, and real-world attack simulation skills. Sign up today to become a certified cybersecurity expert!
Start nowCase Studies
Explore our case stories to see how our solutions create real impact and drive success for our clients.
Trainings
Offensive Hacking with Defensive Tactics
OHSE: Offensive Hacking Security Expert

The OHSE course offers comprehensive training in advanced offensive security techniques, emphasizing practical application through hands-on labs and real-world scenarios. Participants gain expertise in penetration testing, vulnerability assessment, and exploitation methodologies, preparing them to identify and mitigate complex security threats effectively.
Explore TrainingsAWAPT: Advanced Web Application Penetration Testing

AWAPT is designed for professionals aiming to specialize in web application security. The course covers in-depth techniques for identifying and exploiting vulnerabilities in web applications, including automated exploitation using Python and manual testing with tools like Burp Suite.
Explore TrainingsOAES: Offensive API Exploitation and Security

OAES focuses on the security of Application Programming Interfaces (APIs). This advanced, hands-on course provides participants with a custom virtual machine tailored for API penetration testing, equipping them with the skills to identify and address security flaws in modern APIs.
Explore TrainingsOCPT: Offensive Cloud Penetration Testing

The OCPT course delves into cloud computing security, covering topics such as hybrid data storage, cloud platforms like Azure, Google Cloud, and AWS, and cloud penetration testing methodologies. Participants learn to assess and secure cloud infrastructures against potential threats.
Explore TrainingsCTH: Cyber Threat Hunting

CTH training equips individuals with the skills to proactively detect and neutralize cyber threats within networks. The course emphasizes practical techniques for threat identification, analysis, and mitigation, enabling participants to enhance an organization's security posture against advanced persistent threats.
Explore TrainingsSimplify Cybersecurity with
Powerful SaaS Solutions
Unified SaaS platform to automate threat detection, ensure compliance, and gain real-time visibility for proactive security management.
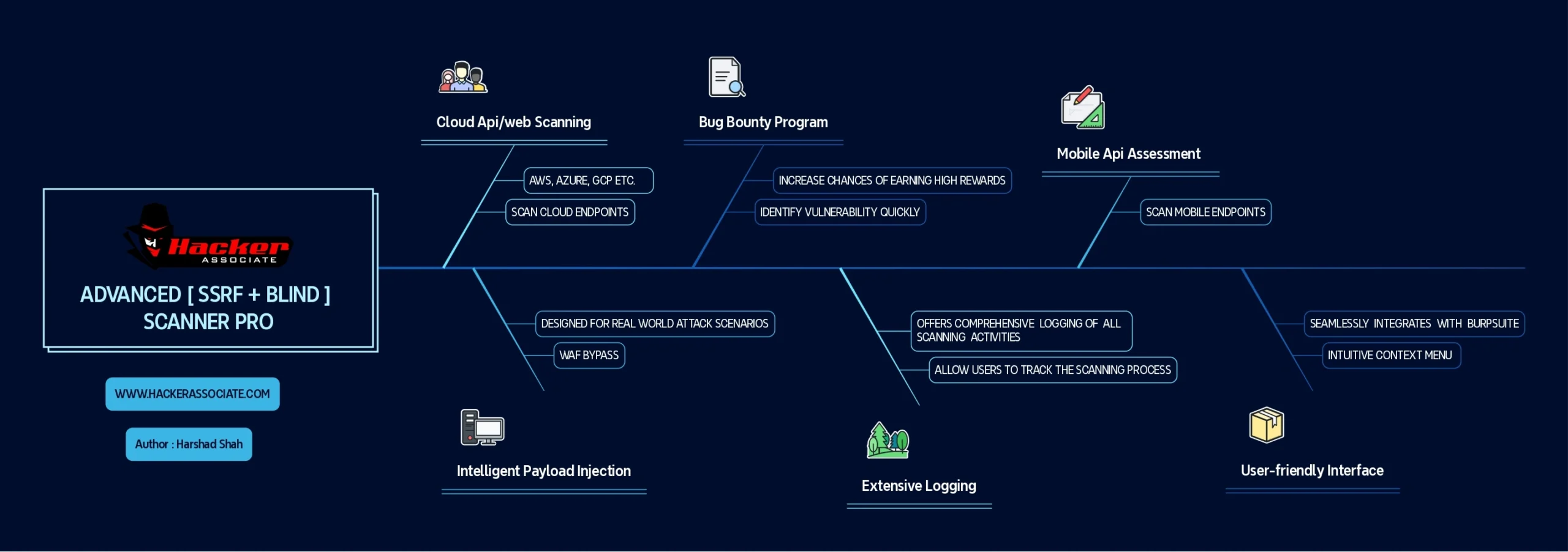
Automated SSRF Scanner Pro
Automated SSRF Scanner by Harshad, a powerful and user-friendly Burp Suite extension designed to streamline the detection of Server-Side Request Forgery (SSRF) vulnerabilities in web applications.
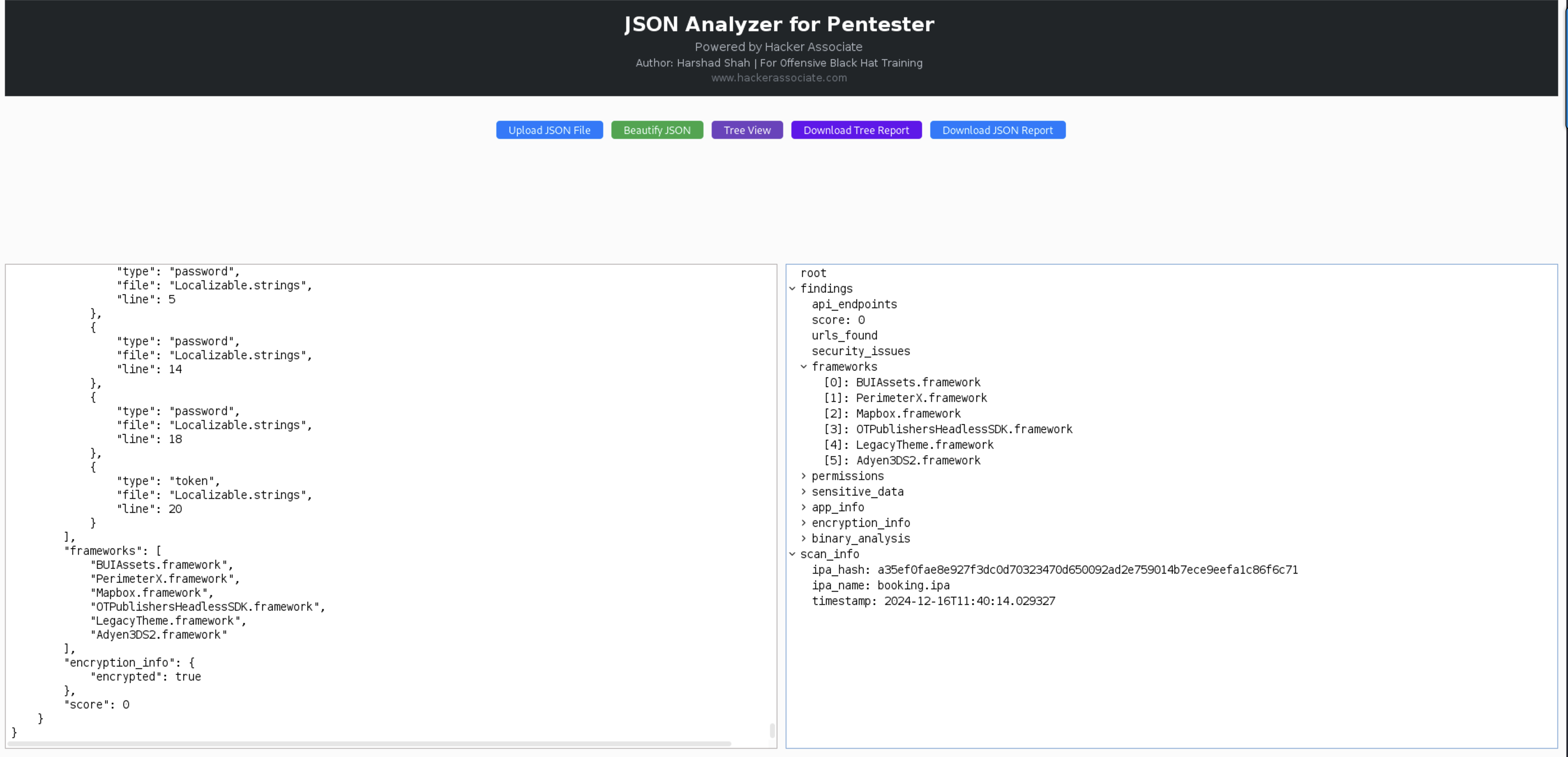
Json Analyzer For Pentester
JSON Analyzer for Pentester is a Burp Suite extension designed to help penetration testers analyze JSON data efficiently. It provides a user-friendly interface for uploading, beautifying, visualizing, and exporting JSON data. This tool is especially useful for analyzing API responses, configuration files, and other JSON-based data during penetration testing.
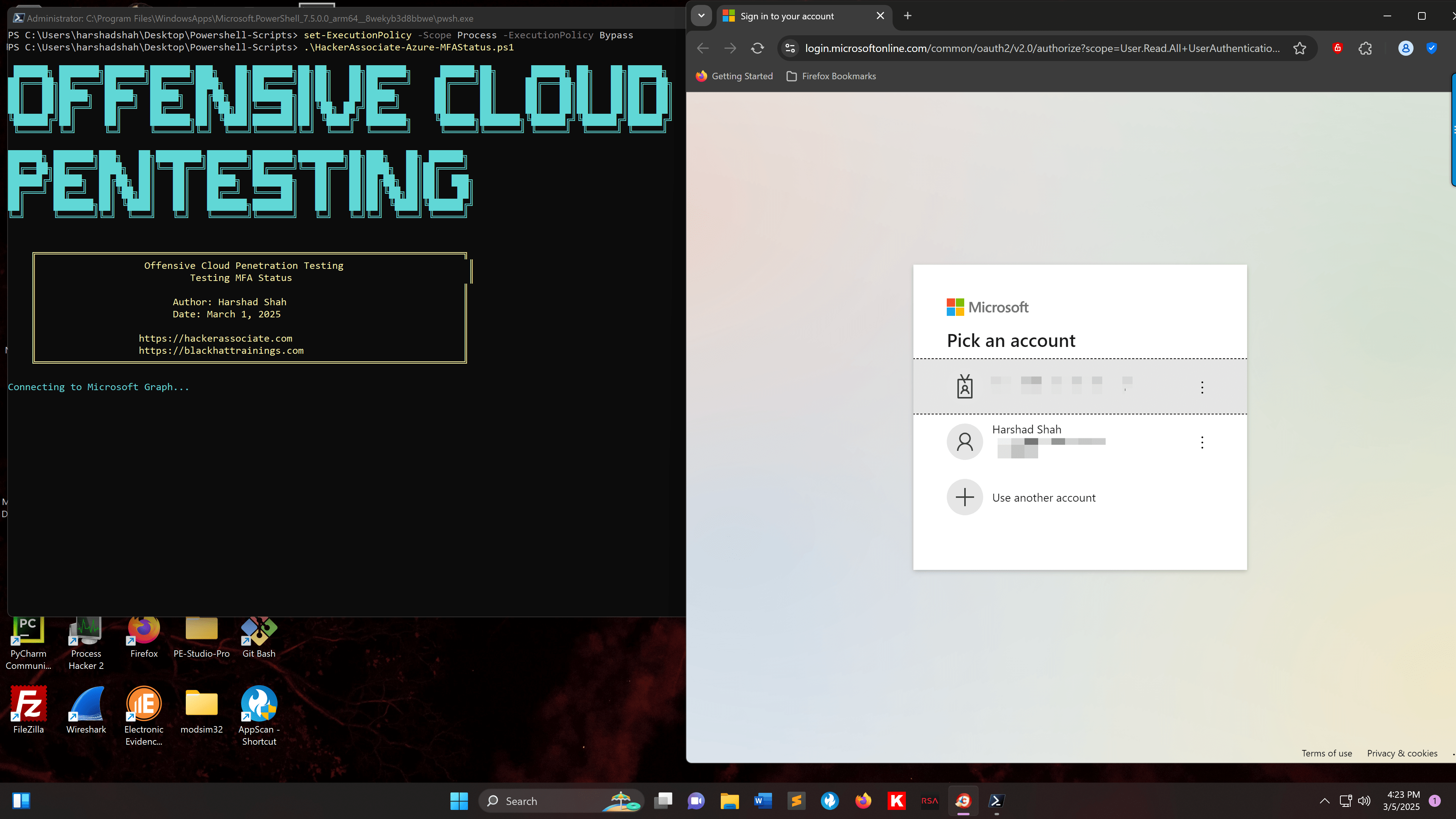
Malicious MFA Takeover Azure
This PowerShell script is designed for malicious purposes to facilitate MFA account takeover. It identifies dormant accounts, and if MFA is not configured, the attacker can initiate an MFA handshake. Once the handshake is completed, they can gain direct access using an authenticator app.
Events
Our Events
TESTIMONIALS
Hear it straight from our clients

Mr. Santosh Panda
Techy

Mr. Shubhitesh
Owner

Ms. Joana Ebert
Student

James Marq
Ceo

Mike Smith
Student
FAQs
Lowering Human Error: Well-informed workers are less prone to human errors, such as falling for phishing scams.
Improved Incident Response: Well-trained employees are more likely to identify potential security threats and report them quickly, allowing timely intervention to prevent breaches.
Creating a Security-Aware Culture: Awareness programs ensure that security becomes an integral part of the company culture, and security practices are followed as a part of everyday work.
Protects sensitive data: Educated employees can protect sensitive data more appropriately and reduce the risk of data breaches.
Maintains Business Continuity: Training and awareness courses educate employees on security best practices, reducing the risk of incidents that could disrupt business operations and ensure business continuity.
Enhanced Customer Trust: Organizations that prioritize cybersecurity through regular training have a great reputation, which ultimately builds customer trust.