IoTHS Syllabus
Module 1:
Introduction to IoT
Module 2:
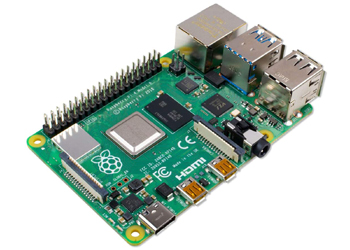
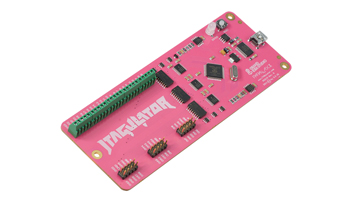
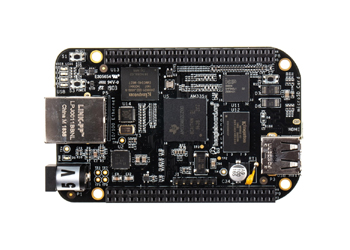
Understanding components, devices, protocol used
Module 3:
Security Policies & Standards
Module 4:
Factors impacting IoT
Module 5:
Understand the architecture, components, and applications of convergent enterprise and industrial IoT
Module 6:
Defining the Security Requirements for Industrial IoT Networks
Module 7:
Introduction to Offensive IoT Exploitation
Module 8:
Vulnerabilities in the Internet of Things
Module 9:
Vulnerabilities in Industrial IoT Networks are being exploited
Module 10:
Database SQL Injection
Module 1:
Defining the Security Process for Industrial IoT Networks
Module 12:
Hardening Industrial IoT Network Devices
Module 13:
Industrial IoT Networks: Implementing Network Infrastructure Security
Module 14:
Packets Injections & simulation of Packet loss (with Wireshark)
Module 15:
BDBA and BDH analysis
Module 16:
Identification of threats from Defenses tool or similar tools
Module 17:
Fuzzing and flooding - how to check memory leaks
Module 18:
Attack surface analysis
Module 19:
Integration or system level Cyber Security testing
Module 20:
Analyzing firmware
Module 21:
Infiltrating Firmware
Module 22:
Emulation of firmware using FAT
Module 23:
Web Application Security for IoT devices
Module 24:
Creating BurpSuite Lab for IoT devices
Module 25:
Conventional Attacks & vectors
Module 26:
Command line exploitation
Module 27:
Analyzing Smart Plugs
Module 28:
Controlling Smart devices bypassing encryption
Module 30:
Buffer overflow on ARM
Module 31:
Exploit writing on ARM
Module 32:
Using radare2 for MIPS binary analysis
Module 33:
Exploitation using GDB remote debugging on MIPS
Module 34:
Embedded Product Penetration Testing
Communication Port Interfaces
- RS 485 Communication Port
- RJ 45 Ethernet IP Port
Communication Protocols Interfaces
- UART
- Modbus Communication
- BACnet
- SNTP
- SMTP
- DNP3
- Ethernet IP
- HTTP or HTTPs
- FTP / FTPs
- TLS
- IPV6
Module 35:
Introduction to UART
Module 36:
Serial interfacing over UART
Module 37:
NAND glitching attack
Module 38:
Building secure IoT system
Module 39:
Port Scanning Result analysis
Module 40:
Identify Top priority risk and Solutions
Module 41:
OWASP IoT Top 10 ( Exploit and Secure)
- Weak, guessable, or hardcoded passwords
- Insecure network services
- Insecure ecosystem interfaces
- Lack of secure update mechanism
- Use of insecure or outdated components
- Insufficient privacy protection
- Insecure data transfer and storage
- Lack of device management
- Insecure default settings
- Lack of physical hardening
Module 42:
Building Trusted identities, data and connectivity
Module 43:
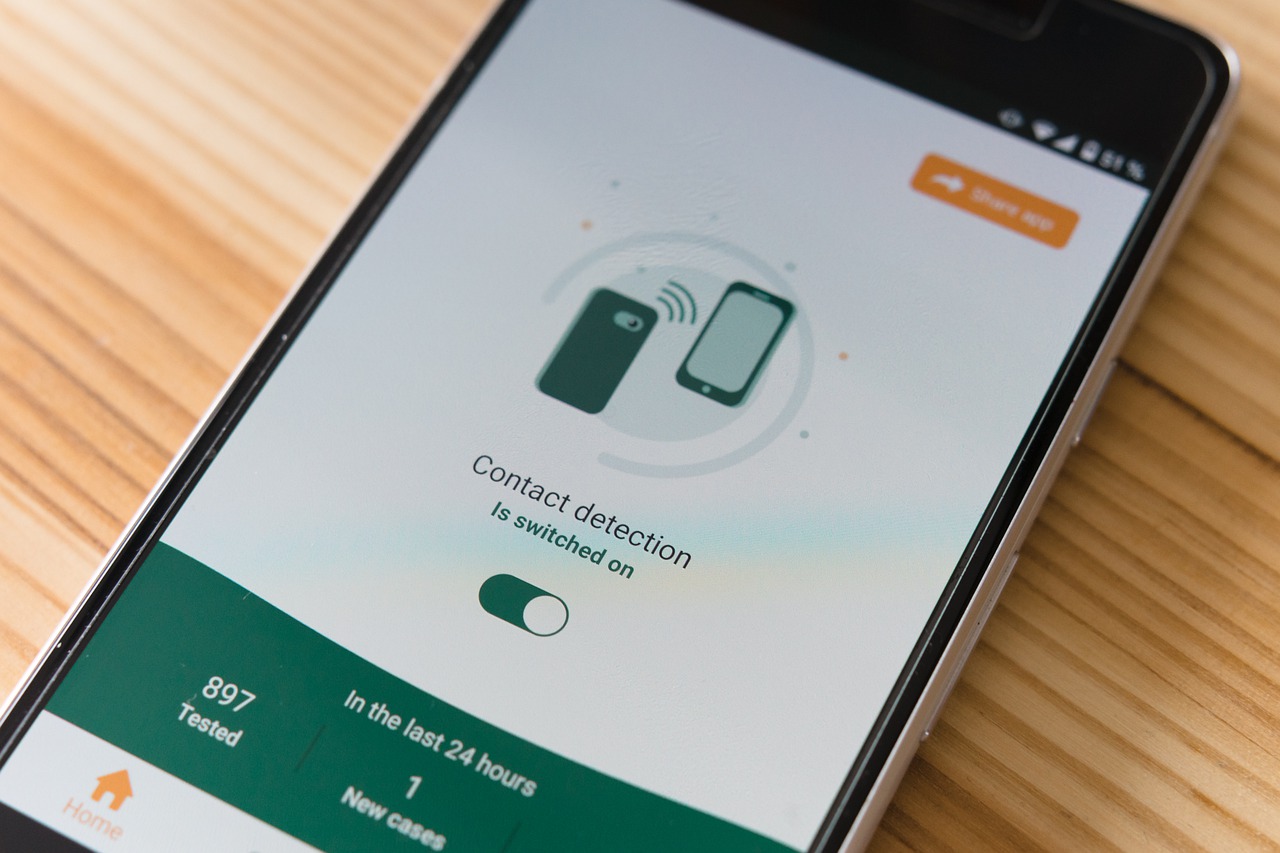
Ensuring Privacy and Confidentiality
Module 44:
Web Server/ Application Interface
Module 45:
Feature based Penetration Testing
- MAC
- RBAC
- Profile based
Module 46:
OWASP TOP 10 for Web Application Security
- Injection
- Broken Authentication
- Broken Authentication
- XML External Entities
- Broken Access Control
- Security Misconfiguration
- Cross-Site Scripting (XSS)
- Insecure Deserialization
- Using Components With Known Vulnerabilities
- Insufficient Logging And Monitoring
Module 47:
Security Management of IoT
Module 48:
Threat Monitoring and Mitigations (Secure design changes verification)
Module 49:
Device Security
Module 50:
Protect Data traffic and Storage
Module 51:
Integrate cryptographic modules in IoT systems
Module 52:
SDLC (Software Development Life Cycle)
Module 53:
Embedded Product – Secure Development Practices and Source Code Review
Module 54:
Secure Coding Practices WRT
- User Access Management,
- Device IP management
Module 55:
Explore Cloud Security in your IoT system
Module 56:
Conclusion and Discussion